Security should be at the top of any business owner’s list of priorities. While cybersecurity often gets the spotlight, physical security is just as critical; after all, if someone can walk in and steal your equipment, all the firewalls in the world won’t help you. Fortunately, technology has made it easier than ever to protect your business from physical threats. Here are some physical security technologies small businesses can use to keep their assets safe.
Advanced Automation Blog
Antivirus is a staple security solution for businesses and everyday PC users, but have you ever considered how it works? By thinking through some of the details, you might gain a greater understanding of how antivirus works, what it does, and why you need to keep it updated. Today, we’re going to discuss just that, starting from square one.
We will always reinforce how critical it is for everyone in any workplace to have a grasp of cybersecurity best practices, regardless of their role or responsibilities. However, based on a survey conducted by UK-based cybersecurity firm Ramsac, this baseline is not being met by a long shot.
Why do we say this? Simple: this survey revealed that one in three adults failed a cybersecurity test designed for 11-year-olds.
You don’t want to get spammed; nobody does. Unfortunately, it happens to EVERYONE, and it’s just getting worse. All this unwelcome correspondence happens over the phone, through email, and especially on social media. In today’s blog, we’ll talk a little bit about how social media puts users at risk and what you can do to keep that risk from becoming a problem for you.
With remote work remaining popular, employees can benefit from flexibility and work-life balance, but at the cost of certain challenges on the business side. The big one is security, as your network ends up spread out across multiple locations rather than siloed in-house. Here are three rules you should consider when planning out how to approach remote work.
Think about the apps you use daily—Google Drive, Netflix, Spotify, even Instagram. All of these run on cloud-based services, which basically means they store and process everything online instead of relying on one physical device. Businesses, big and small, are making the same shift because, honestly, it just makes sense. Let’s take a look at why you should be looking to use cloud services in your business.
Text messages are great. They’re a quick and effective means for us all to communicate.
Unfortunately, this does bring some downsides, too… namely, they’re a relatively simple means for a scammer to spread their attacks. Let’s discuss why this is so dangerous and how you can identify and avoid these threats.
When hackers steal data, they don't just sit on it. Sometimes they delete it, but most of the time, they sell it or use it for illegal activities. A lot of this stolen data ends up on the Dark Web, a hidden part of the Internet where people do shady things. That's why it's so important to keep an eye on the Dark Web to protect your business.
Have you ever suspected that a hacker could silently observe your email interactions with your clients and your staff? If you manage your own email infrastructure, we want to highlight the importance of email encryption. Encryption keeps your business’ email communications secure and compliant so you can worry less about security and privacy to focus more on running your business.
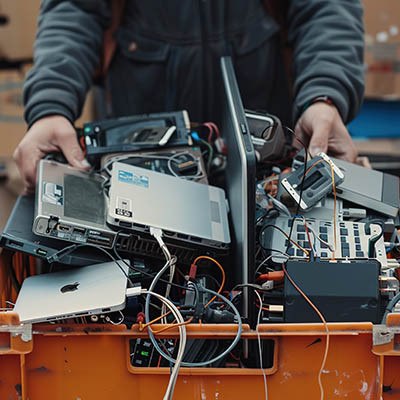
So you got a new computer for a holiday gift. That’s great! We’re excited that you’re excited. But you also need to consider how you are going to dispose of your old device and how to do so in a safe way. Today, we want to discuss how you can safely discard, or potentially even reuse, your old device so you don’t put your data at risk.
To keep your business running smoothly, even if something goes wrong—like a power outage, cyberattack, or other disaster—you need a reliable way to protect your data. That’s where data backup comes in. It’s important to make sure your backup is thorough and trustworthy so you can recover if things go south.
Imagine giving every single person you work with a key to your house. Would you do it? Probably not, right? What if someone lost their key or had it stolen? You wouldn’t want to take that risk.
So, it stands to reason that if you can’t trust the people you work with every day with a key to your house, you wouldn’t want them to have access to all of your data; or your business’.
Every business relies on technology to function. Some wouldn’t be able to deliver any value to their customers without it, while others would be severely hindered if they suffered a data breach. For this reason, cybersecurity has to be a priority. In today’s blog, we will discuss five issues that business owners run into that can muddle their cybersecurity efforts.
Businesses of every size need to prioritize their security. This fact has not changed and will not change anytime soon. What has changed, however, are the recommended ways to approach this security.
Today, we wanted to review the history of today’s predominant cybersecurity advice and explore how the zero-trust security model applies.
Can you tell the difference between your colleagues and a scammer with access to their email account? This is essentially what a business email compromise attack involves—a scammer initiates a phishing scheme using an internal mode of communication. These scams are also observed in schools, making them dangerous in the education sector.
Would you feel safe staying at a hotel that, instead of unique locks, each door used the same key as all of the others? Probably not—because if someone got in, they could take whatever they wanted. That’s similar to how old-school cybersecurity worked. Once someone got into a company’s network, they could access almost everything, making it easy for hackers to steal information. But today, many businesses use a better security framework called zero-trust security. In today’s blog, we discuss what zero-trust security is and why it’s safer.